Ghost of Tsushima Director’s Cut, prezzo IRRISORIO per PS5
Multicavo 4 in 1, ricarichi qualunque dispositivo SUBITO (6€)
Caricatore multiplo per la tua comodità: ricarica rapida e 4 USB
Echo Show 8 in GRAN sconto, approfitta del 40% per portarlo a casa
New Google Workspace features to help solo business owners
Over the past few years, we’ve seen more people forging their own path and turning their personal passions into businesses. These individual business owners, sometimes called “solopreneurs,” wear many hats as they run and grow their businesses: salesperson, marketer, accountant, the list goes on.
That’s why one year ago, we launched Google Workspace Individual as a new offering to help these solo business owners grow their businesses with the familiar apps they’re likely already using in their personal life. We’ve heard from customers that Google Workspace Individual helps them focus their time on doing what they love — like meeting with customers and designing personalized services — and less time on recurring tasks like scheduling appointments and sending emails. Since launch, we’ve delivered a number of improvements to provide even more value to customers, and today we’re announcing what’s coming next – electronic signatures right within Google Docs.
Coming soon: Easily sign important documents right in Google Docs
Whether you’re an event planner or digital creator, it can be a challenge to stay on top of contracts and customer agreements that need to be signed as you’re constantly context switching and jumping between different apps to get work done. That’s why we’re natively integrating eSignature in Google Docs, so you can quickly execute agreements from the familiar interface of Docs without having to switch tabs or apps.

Coming soon: Easily request electronic signatures directly in Google Docs
eSignature in Google Docs will take advantage of the same secure-by-design infrastructure and built-in protections Google uses to help secure your information and safeguard your privacy. Let’s take a look at how eSignature can help you create agreements:
- Collaborate in documents: Collaborate on changes directly in Google Docs with comments and suggestions — no need to export the file to send a draft contract over email.
- Add fields to documents: Within the familiar Google Docs interface, you can easily drag and drop signature and date fields in branded documents you create.
- Request a signature: Once you resolve all comments and suggestions, requesting a signature is as easy as sharing a file in Drive.
- Add signatures: When ready to sign, the signee can easily add their signature, no downloads needed. Once the signature is added, a completed PDF contract is emailed to both parties.
- Monitor and track progress: Quickly see the status of pending signatures and easily find completed, signed contracts.
- Create copies of contracts: For signature workflows that need to be repeated regularly, you can streamline the process by creating copies of existing contracts and then modifying as needed.
eSignature in Google Docs is coming soon in Beta to Google Workspace Individual users and is the latest in a series of improvements we’ve announced for the subscription in the past year. If you’re already using a dedicated eSignature solution, Google Workspace integrates with a number of leading providers. Learn more about how these eSignature and other integrations can help you optimize your workspace on our blog post.
ICYMI: Google Workspace Individual updates from this past year
Email marketing updates for engaging campaigns
For any business, it’s vital to connect with customers and prospects, both on a one-to-one basis and at a large scale. Google Workspace Individual makes it easy to do both, so you can easily send communications like monthly newsletters and also offer items like scheduled consultations.

Create and send customized marketing emails from Gmail
To help you reach many customers at once, last year we added a way to run simple email campaigns directly in Gmail. We started first by providing professionally designed templates that you can customize with your own branding and images in just a few clicks. Then earlier this year, we added multi-send, which allows you to deliver individual emails to a large number of recipients with a unique unsubscribe link for each recipient. With the combination of these improvements, it’s easy to make communications as targeted as you like, because you can create multiple email mailing lists within Google Contacts for different audiences and easily tailor the message to each audience. Gmail layouts and multi-send are generally available in Google Workspace Individual today.
Appointment scheduling updates for easier bookings
For scheduling in-person appointments or virtual meetings, Google Calendar helps streamline the appointment scheduling process and avoid back-and-forth communication to find a time that works. Since launching, we’ve made a number of enhancements that improve the experience for both the business owner and scheduler, including the ability to:
- Help prevent no-shows by customizing the timing of reminder emails and having users verify their email before booking for added security.
- Reflect your operational needs by setting flexible appointment durations, adding buffer time between appointments and limiting the number of bookings per day.
- Easily update your availability with one-off exceptions like regional holidays and customizable start and end dates.

Get your own professional booking page that stays up to date
Customized appointment scheduling with the above features are generally available in Google Workspace Individual today, on the web and your mobile device.
Google Meet updates for your customer and partner calls
Once an appointment is on the books and it’s time to connect, Google Meet provides an easy way for you to deepen customer and partner relationships through secure video meetings. Helpful features in Meet ensure you can be clearly seen and heard. Noise cancellation removes background distractions like barking dogs, while low-light mode automatically adjusts your video in poorly lit settings. Here are a few notable Meet announcements from this past year:
- Mimic taking your call from a real-life cafe or condo with immersive backgrounds.
- Filter out the echoes in spaces with hard surfaces so that you can have conference-room audio quality whether you’re in a basement, a kitchen, or a big empty room.
- Clearly see participants on a call while you’re presenting or multi-tasking with picture-in-picture on Chrome browsers.
- Review your forecast or business proposal with meetings directly in Docs, Sheets and Slides.

Quickly join a Google Meet call from Google Docs, Sheets and Slides
Sign up today to take advantage of promotional pricing
Save 20% until October 2022
Paper Mario: The Origami King a piccolo prezzo, tuo con 46€
10 test rapidi antigenici anti Covid-19 OFFERTONA Amazon (17€)
Mini ventilatore USB: sempre FRESCO anche fuori casa
Google for Mexico: Economic recovery through technology
During the pandemic, different technological tools allowed us to stay connected, collaborate and find the best responses to overcome the challenges in front of us.
As we move forward, we want to become Mexico’s trusted technology ally and contribute to the country with programs, products and initiatives that promote economic, social and cultural development. Today, at our second Google for Mexico event, we aim to accelerate the country’s economic recovery, helping people find more and better jobs, making it easier for businesses to grow, reduce the gender gap and promote financial inclusion.
Improving Mexicans’ lives through technology
In collaboration with the Ministry of Public Education, we helped students across the country to continue their school year by providing more than 20 million free Google for Education accounts. We have trained more than 1.9 million people in Mexico through Grow with Google and Google.org grants. And we have worked together with the Ministry of Tourism to create a joint strategy to digitize the travel sector, and partnered with the Ministry of Economy on gender gap reduction projects and a technological innovation program for manufacturing companies in the southeast region of the country.
According to a study we conducted with AlphaBeta, in 2021 we estimated that companies in the country obtained annual economic benefits worth more than $7.7 billion dollars from Google products (Google Search & Ads, AdSense, Google Play and YouTube), approximately three times the impact in 2018 ($2.3 billion dollars).
Today, more people in the world are using their smartphones to save credit and debit cards and to buy new things. Over the last few years, we have seen rapid digitization of essentials that we carry with us every day, such as car keys, digital IDs and vaccine records.
That’s why we are announcing that Mexico is part of the global launch of Google Wallet on Android and Wear OS. Google Wallet will initially launch with support for payment cards and loyalty passes and eventually expand to new experiences like transit and event tickets, boarding passes, car keys and digital IDs.
$10 million from Google.org
Mexico’s Southeast region is home to more than 50% of the country’s indigenous population; it is also a place affected by poverty and with big social vulnerability. Google.org, the philanthropic arm of Google, is allocating $10 million — the largest amount of funding provided by the organization in the country — to this region’s transformation. This initiative will mostly benefit women during the upcoming three years, supporting programs focused on promoting economic opportunities that accelerate financial inclusion, reducing the gender gap.

Women from Mexico’s Southeast region will benefit from Google.org 10 million dollars fund through local and regional NGOs.
Technology as a booster for jobs
In 2019, during the first edition of Google for Mexico, we announced the launch of Google Career Certificates alongside a grant of $1.1 million for International Youth Foundation Mexico (IYF). Through this grant, IYF has trained 1,200 young people. Seventy percent of the graduates managed to get a new job, while the participants who were already employed raised their income by more than 30%. To expand this initiative, and as part of the $10M fund to support Mexico’s Southeast region, we are announcing a $2 million grant to support IYF to take their project into the region and train 2300 women from the community.
Supporting the news industry
In late 2020, we launched Google News Showcase, an initiative that offers a better experience for readers and news editors. Google News Showcase is a licensing program to pay publishers for high-quality content. This program will help participating publishers monetize their content through an enhanced storytelling experience that lets people go deeper into more complex stories and stay informed about different issues and interests.
Today we are announcing the beginning of negotiations with local media to soon launch a News Showcase in México. We are excited to continue contributing to the country’s media ecosystem, and offer our users relevant, truthful and quality information on local, national and international news.

Google News Showcase will bring a better experience for readers and news publishers in Mexico.
Preserving and promoting native languages
Every 14 days, a language becomes extinct. This means that out of the 7,000 existing tongues in the world, more than 3,000 are in danger of vanishing. To support the efforts of groups dedicated to language preservation, Google Arts & Culture is collaborating with partners around the world to launch Woolaroo, an experiment that uses machine learning to identify objects and show them in native languages.
Through their mobile cameras, users can take a photo or check their surroundings to receive a translation, and its correct pronunciation. In the beginning, Woolaroo could do this in 10 languages, and today seven more have been added, including Maya and Tepehua.

Woolaroo, a language preservation experiment powered by machine learning, will include ancestral languages Maya and Tepehua.
At Google, we believe technology is the fuel to be helpful for Mexicans across the country, providing intelligent solutions for millions of people.
Auricolari Bluetooth a 19€ e con tutto a posto giusto: 45 ore NO STOP
GitHub e i comportamenti “tossici” degli sviluppatori
Da uno studio sulla tossicità nel Web emergerebbe come in GitHub siano gli sviluppatori con esperienza ad adottare i comportamenti peggiori
Leggi GitHub e i comportamenti “tossici” degli sviluppatori
Mahima Pushkarna is making data easier to understand
Five years ago, information designer Mahima Pushkarna joined Google to make data easier to understand. As a senior interaction designer on the People + AI Research (PAIR) team, she designed Data Cards to help everyone better understand the contexts of the data they are using. The Data Cards Playbook puts Google’s AI Principles into practice by providing opportunities for feedback, relevant explanations and appeal.
Recently, Mahima’s paper on Data Cards (co-written with Googlers Andrew Zaldivar and Oddur Kjartansson) was accepted to the ACM Conference on Fairness, Accountability and Transparency (ACM FAccT). Let’s catch up with her and find out more about what brought her to Google.
How did your background lead you to the work you’re doing now?
I’ve always been fascinated by conjuring up solutions to things. The kind of questions that I’ve found meaningful are those that are never truly solved, or never have one correct answer. (The kind of questions that exasperate us!) Those have been the problems I am always drawn towards.
Early in my career, I realized the power in visualizing data, but spreadsheets were intimidating. I wondered how design could make communicating complexity easier. So I found myself in grad school in Boston studying information design and data visualization. I focused on how people experience data and how our relationships to each other and our contexts are mediated.
I joined Google Brain as the first visual designer in a full-time capacity, though I had no background in artificial intelligence or machine learning — this was the deep end of the pool. This opened up the space to explore human-AI interaction, and make AI more accessible to a broader class of developers. At PAIR, my work focuses on making information experiences more meaningful for developers, researchers and others who build AI technologies.
What’s it like to have a unique background as a designer on a technical AI research team?
When you’re an engineer and immersed in building technology, it’s easy to assume everyone has a similar experience to your own — especially when you’re surrounded by peers who share your expertise. The actual user experience is very personal and varies drastically across users and contexts. That particular clarity is what designers bring to the table.
I’ve been able to engage my engineering and research colleagues with simple, people-centered questions right in the very beginning. How are people using an AI tool? What are they learning from it? Who else might be involved in the conversation? Do they have the proficiency we assume they have?
Pull quote: “Identifying what we don’t know about data is just as important as articulating what we do know.”
How did you begin designing Data Cards?
This project started when I was working on another visualization toolkit, Facets, to communicate the skews and imbalances within datasets to help machine learning practitioners make informed decisions. At the time, transparency was a moving target. Andrew, Tulsee Doshi and I started to proactively think about fairness in data, and saw a huge gap in the documentation of human decisions that dot a dataset’s lifecycle.
This “invisible” information shapes how we use data and the outcomes of models trained on them. For example, a model trained on a dataset that captures age in just two or three buckets will have very different outcomes compared to a dataset with ten buckets. The goal of Data Cards is to make both visible and invisible information about datasets available and simple to understand, so people from a variety of backgrounds can knowledgeably make decisions.
As we cover in our FAccT paper, Andrew and Oddur and I arrived at two insights. The first is that identifying what we don’t know about data is just as important as articulating what we do know. In capturing these nuances, it is possible to narrow those knowledge gaps before even collecting data. The second thing that surprised us was the sheer number of people involved in a dataset’s life cycle, and how fragile knowledge is. Context is easily lost in translation both between and within teams, across documents, emails, people and time.
Data Cards stand on the shoulders of giants, like Data Sheets (Gebru, et al.) and Model Cards (Mitchell et al.). We’ve been immensely lucky to have had the support of many original authors on these seminal papers that have paved our path to FAccT.
How do you hope the paper is used across the tech industry?
Imagine a world in which finding verifiable information about the motivations of a dataset’s creators or performance of a model is as easy as learning about the ethical beliefs of a celebrity or the rating of a movie. Our vision for Data Cards is that they become a cultural mainstay — invisible, but their absence would be missed by ML practitioners.
In this paper, we introduce frameworks that other teams can use in their work. Alongside that, we’ve open-sourced the Data Cards Playbook, so we’re trying to lower the barrier to access in every way possible.
Countering hack-for-hire groups
As part of TAG’s mission to counter serious threats to Google and our users, we’ve published analysis on a range of persistent threats including government-backed attackers, commercial surveillance vendors, and serious criminal operators. Today, we’re sharing intelligence on a segment of attackers we call hack-for-hire, whose niche focuses on compromising accounts and exfiltrating data as a service.
In contrast to commercial surveillance vendors, who we generally observe selling a capability for the end user to operate, hack-for-hire firms conduct attacks themselves. They target a wide range of users and opportunistically take advantage of known security flaws when undertaking their campaigns. Both, however, enable attacks by those who would otherwise lack the capabilities to do so.
We have seen hack-for-hire groups target human rights and political activists, journalists, and other high-risk users around the world, putting their privacy, safety and security at risk. They also conduct corporate espionage, handily obscuring their clients’ role.
To help users and defenders, we will provide examples of the hack-for-hire ecosystem from India, Russia, and the United Arab Emirates and context around their capabilities and persistence mechanisms.
How Hack-For-Hire Operations Work
The hack-for-hire landscape is fluid, both in how the attackers organize themselves and in the wide range of targets they pursue in a single campaign at the behest of disparate clients. Some hack-for-hire attackers openly advertise their products and services to anyone willing to pay, while others operate more discreetly selling to a limited audience.
For example, TAG has observed Indian hack-for-hire firms work with third party private investigative services — intermediaries that reach out for services when a client requires them — and provide data exfiltrated from a successful operation. This is detailed in depth in today’s Reuters investigation into the Indian hack-for-hire ecosystem. We have also observed Indian hack-for-hire firms work with freelance actors not directly employed by the firms themselves.
The breadth of targets in hack-for-hire campaigns stands in contrast to many government-backed operations, which often have a clearer delineation of mission and targets. A recent campaign from an Indian hack-for-hire operator was observed targeting an IT company in Cyprus, an education institution in Nigeria, a fintech company in the Balkans and a shopping company in Israel.
Recent Hack-for-Hire Campaigns
India
Since 2012, TAG has been tracking an interwoven set of Indian hack-for-hire actors, with many having previously worked for Indian offensive security providers Appin and Belltrox.
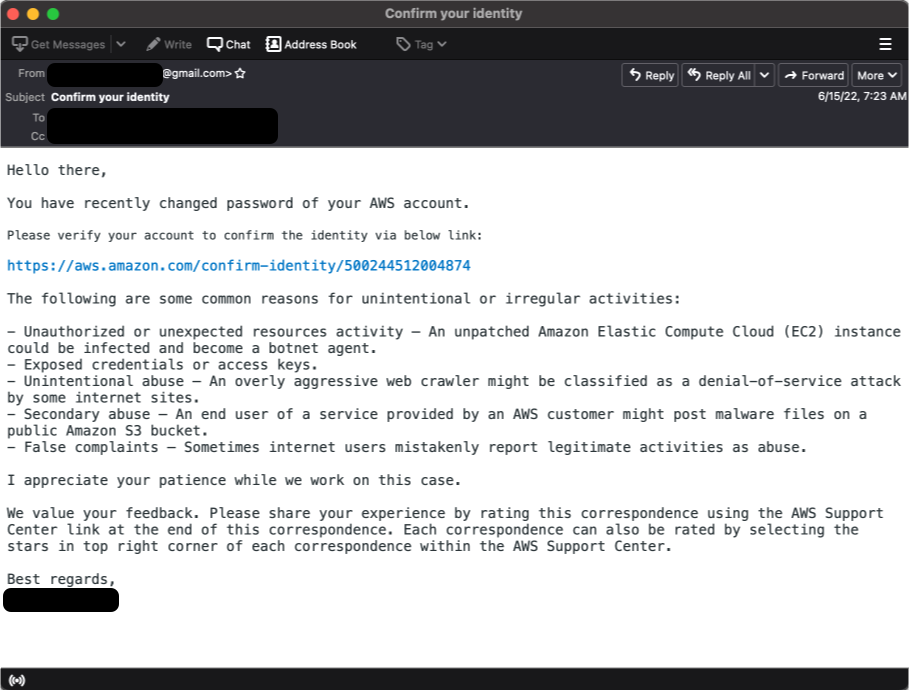
One cluster of this activity frequently targets government, healthcare, and telecom sectors in Saudi Arabia, the United Arab Emirates, and Bahrain with credential phishing campaigns. These credential phishing campaigns have ranged from targeting specific government organizations to AWS accounts to Gmail accounts.

Sample AWS phishing email

Sample AWS phishing page
TAG has linked former employees of both Appin and Belltrox to Rebsec, a new firm that openly advertises corporate espionage as an offering on its company website.
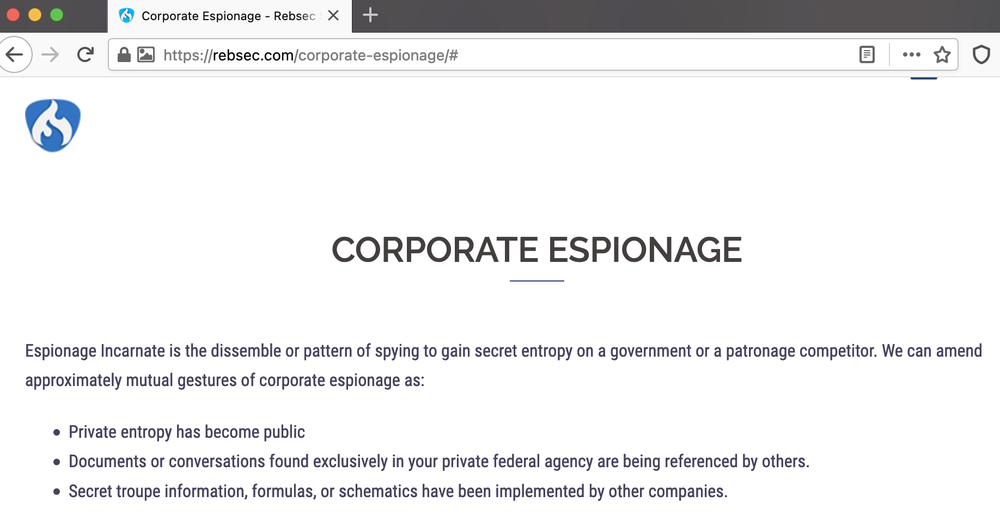
Rebsec’s offerings as per the company’s website
Russia
While investigating a 2017 credential phishing campaign that targeted a prominent Russian anti-corruption journalist, we discovered the Russian attacker targeting other journalists, politicians across Europe, and various NGOs and non-profit organizations. But what stuck out during this investigation was the breadth of targeting, which also included individuals that had no affiliation with the selected organizations, and appeared to be regular, everyday citizens in Russia and surrounding countries. This hack-for-hire actor has been publicly referred to as ‘Void Balaur’.
These campaigns were similar regardless of target, consisting of a credential phishing email with a link to an attacker-controlled phishing page. The lures ranged from fake Gmail and other webmail provider notifications to messages spoofing Russian government organizations. After the target account was compromised, the attacker generally maintained persistence by granting an OAuth token to a legitimate email application like Thunderbird or generating an App Password to access the account via IMAP. Both OAuth tokens and App Passwords are revoked when a user changes their password.
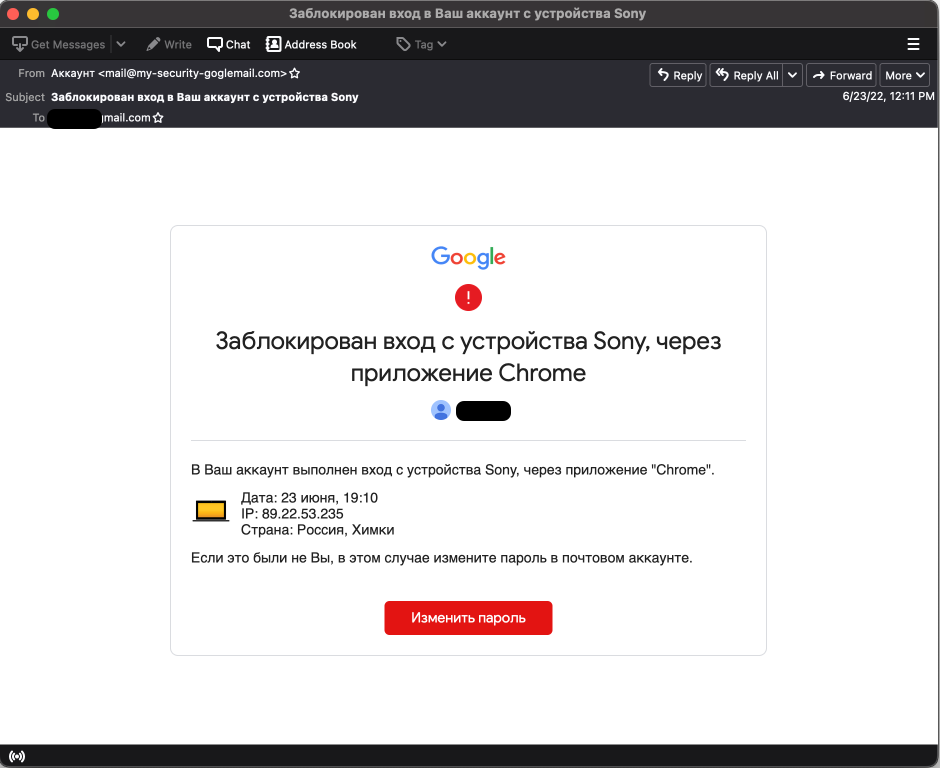
Russian hack-for-hire phishing email
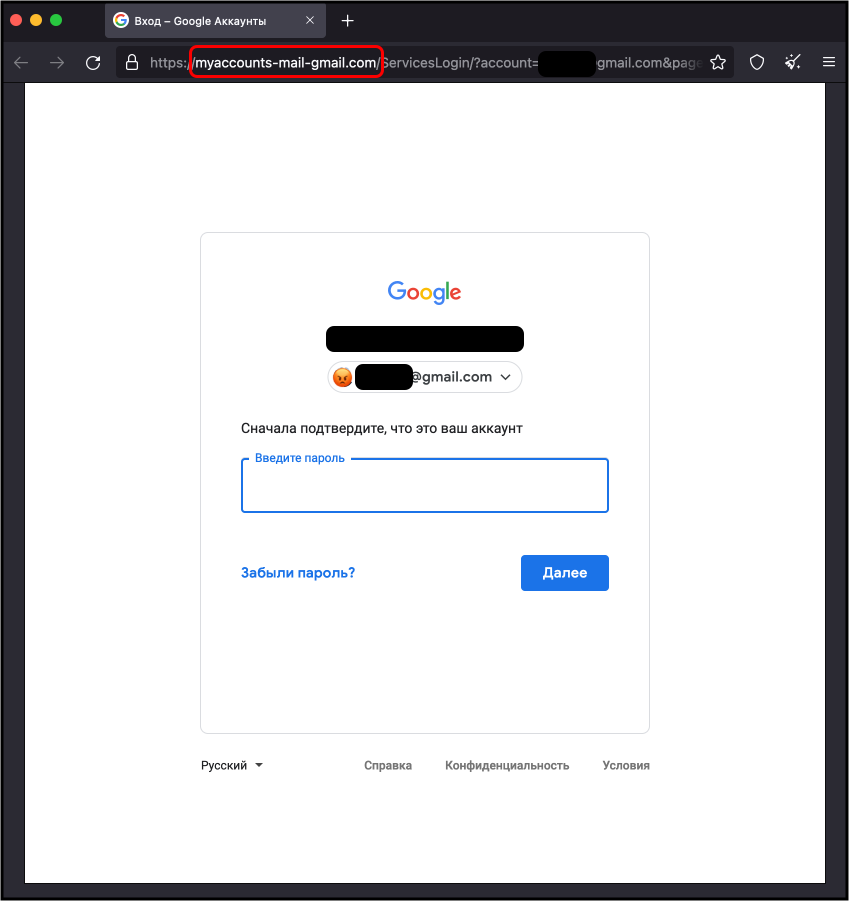
Russian hack-for-hire phishing site
During our early investigation, TAG discovered the attacker’s public website (no longer available) advertising account hacking capabilities for email and social media services. The site claimed to have received positive reviews on Russian underground forums such as Dublikat and Probiv.cc. Over the past five years, TAG has observed the group targeting accounts at major webmail providers like Gmail, Hotmail, and Yahoo! and regional webmail providers like abv.bg, mail.ru, inbox.lv, and UKR.net.

Pricing list from hacknet-service.com in 2018
United Arab Emirates
TAG is also tracking a hack-for-hire group now based in the United Arab Emirates that is mostly active in the Middle East and North Africa. They have primarily targeted government, education, and political organizations including Middle East focused NGOs in Europe and the Palestinian political party Fatah. Amnesty International has also reported on their campaigns.
The group commonly uses Google or OWA password reset lures to steal credentials from targets, often using the MailJet or SendGrid API to send phishing emails. Unlike many hack-for-hire actors that use open source phishing frameworks like Evilginx or GoPhish, this group uses a custom phishing kit that utilizes Selenium, a self described ‘suite of tools for automating web browsers.’ Previously described by Amnesty, this phishing kit has remained under active development over the past five years.

Google Security Alert phishing page
After compromising an account, the actor maintains persistence by granting themselves an OAuth token to a legitimate email app like Thunderbird, or by linking the victim Gmail account to an attacker-owned account on a third-party mail provider. The attacker would then use a custom tool to download the mailbox contents via IMAP.
This group also has links to the original developers of H-Worm, also known as njRAT. In 2014, Microsoft filed a civil suit against the developer, Mohammed Benabdellah, for the development and dissemination of H-Worm. Benabdellah, who also goes by the moniker Houdini, has been actively involved in the day-to-day development and operational deployment of the credential phishing capabilities used by this group since its inception.
Protecting Our Users
As part of our efforts to combat serious threat actors, we use results of our research to improve the safety and security of our products. Upon discovery, all identified websites and domains were added to Safe Browsing to protect users from further harm. We encourage any high risk user to enable Advanced Protection and Google Account Level Enhanced Safe Browsing and ensure that all devices are updated. Additionally, our CyberCrime Investigation Group is sharing relevant details and indicators with law enforcement.
TAG is committed to sharing our findings as a way of raising awareness with the security community, and with companies and individuals that might have been targeted. We hope that improved understanding of the tactics and techniques will enhance threat hunting capability and lead to stronger user protections across the industry.
With contributions from Winnona DeSombre
Indicators of Compromise
UAE hack-for-hire Group Domains:
- myproject-login[.]shop
- mysite-log[.]shop
- supp-help[.]me
- account-noreply3[.]xyz
- goolge[.]ltd
- goolge[.]help
- account-noreply8[.]info
- account-server[.]xyz
- kcynvd-mail[.]com
- mail-goolge[.]com
- kcynve-mail[.]com
Indian hack-for-hire Group Domains:
- dtiwa.app[.]link
- share-team.app[.]link
- mipim.app[.]link
- processs.app[.]link
- aws-amazon.app[.]ink
- clik[.]sbs
- loading[.]sbs
- userprofile[.]live
- requestservice[.]live
- unt-log[.]com
- webtech-portal[.]com
- id-apl[.]info
- rnanage-icloud[.]com
- apl[.]onl
- go-gl[.]io
Russian hack-for-hire Group Domains:
- login-my-oauth-mail[.]ru
- oauth-login-accounts-mail[.]ru
- my-oauth-accounts-mail[.]ru
- login-cloud-myaccount-mail[.]ru
- myaccounts-auth[.]ru
- security-my-account[.]ru
- source-place-preference[.]ru
- safe-place-smartlink[.]ru
- safe-place-experience[.]ru
- preference-community-place[.]ru
Staying safe online with our updated Google Password Manager
Strong, unique passwords are key to helping keep your personal information secure online. That’s why Google Password Manager can help you create, remember and autofill passwords on your computer or phone: on the web in Chrome, and in your favorite Android and iOS apps.
Today we’ve started rolling out a number of updates that help make the experience easier to use, with even stronger protections built in.
A consistent look and feel, across web and apps
We’re always grateful for feedback, and many of you have shared that managing passwords between Chrome and Android has been confusing at times: “It’s the same info in both places, so why does it look so different?” With this release, we’re rolling out a simplified and unified management experience that’s the same in Chrome and Android settings. If you have multiple passwords for the same sites or apps, we’ll automatically group them. And for your convenience, you can create a shortcut on your Android home screen to access your passwords with a single tap.
You can now add a shortcut to Google Password Manager to your Android homescreen.
More powerful password protections
Google Password Manager can create unique, strong passwords for you across platforms, and helps ensure your passwords aren’t compromised as you browse the web. We’re constantly working to expand these capabilities, which is why we’re giving you the ability to generate passwords for your iOS apps when you set Chrome as your autofill provider.

You can now create strong passwords on your computer or mobile, on any operating system.
Chrome can automatically check your passwords when you enter them into a site, but you can have an added layer of confidence by checking them in bulk with Password Checkup. We’ll now flag not only compromised credentials, but also weak and re-used passwords on Android. If Google warns you about a password, you can now fix them without hassle with our automated password change feature on Android.

For your peace of mind, Password Checkup on Android can flag compromised, weak and reused passwords.
To help protect even more people, we’re expanding our compromised password warnings to all Chrome users on Android, Chrome OS, iOS, Windows, MacOS and Linux.
Simplified access and password management
Google built its password manager to stay out of your way — letting you save passwords when you log in, filling them when you need them and ensuring they aren’t compromised. However, you might want to add your passwords to the app directly, too. That’s why, due to popular demand, we’re adding this functionality to Google Password Manager on all platforms.

Adding your passwords directly is now possible on all platforms.
In 2020, we announced Touch-to-Fill to help you fill your passwords in a convenient and recognizable way. We’re now bringing Touch-to-Login to Chrome on Android to make logging in even quicker by allowing you to securely log in to sites directly from the overlay at the bottom of your screen.
Touch-to-Login signs you in directly from a recognizable overlay.
Many of these features were developed at the Google Safety Engineering Center (GSEC), a hub of privacy and security experts based in Munich, so Guten Tag from the team! Of course, our efforts to create a safer web are a truly global effort – from our early work on 2-step verification, to our future investments in technologies like passkeys – and these updates that we are rolling out over the next months are an important part of that work.
HUAWEI MateView GT: display 2K e frequenza a 165 HZ ad un prezzo BOMBA su Amazon
Uno dei migliori monitor con display 2K sul mercato grazie alla qualità dei suoi componenti, ora in promo su Amazon: risparmia 140 sul prezzo d’acquisto
Leggi HUAWEI MateView GT: display 2K e frequenza a 165 HZ ad un prezzo BOMBA su Amazon