Google’s Threat Analysis Group tracks actors involved in disinformation campaigns, government backed hacking, and financially motivated abuse. We have a long-standing policy to send you a warning if we detect that your account is a target of government-backed phishing or malware attempts. So far in 2021, we’ve sent over 50,000 warnings, a nearly 33% increase from this time in 2020. This spike is largely due to blocking an unusually large campaign from a Russian actor known as APT28 or Fancy Bear.
We intentionally send these warnings in batches to all users who may be at risk, rather than at the moment we detect the threat itself, so that attackers cannot track our defense strategies. On any given day, TAG is tracking more than 270 targeted or government-backed attacker groups from more than 50 countries. This means that there is typically more than one threat actor behind the warnings.
In this blog, we explore some of the most notable campaigns we’ve disrupted this year from a different government-backed attacker: APT35, an Iranian group, which regularly conducts phishing campaigns targeting high risk users. This is the one of the groups we disrupted during the 2020 US election cycle for its targeting of campaign staffers. For years, this group has hijacked accounts, deployed malware, and used novel techniques to conduct espionage aligned with the interests of the Iranian government.
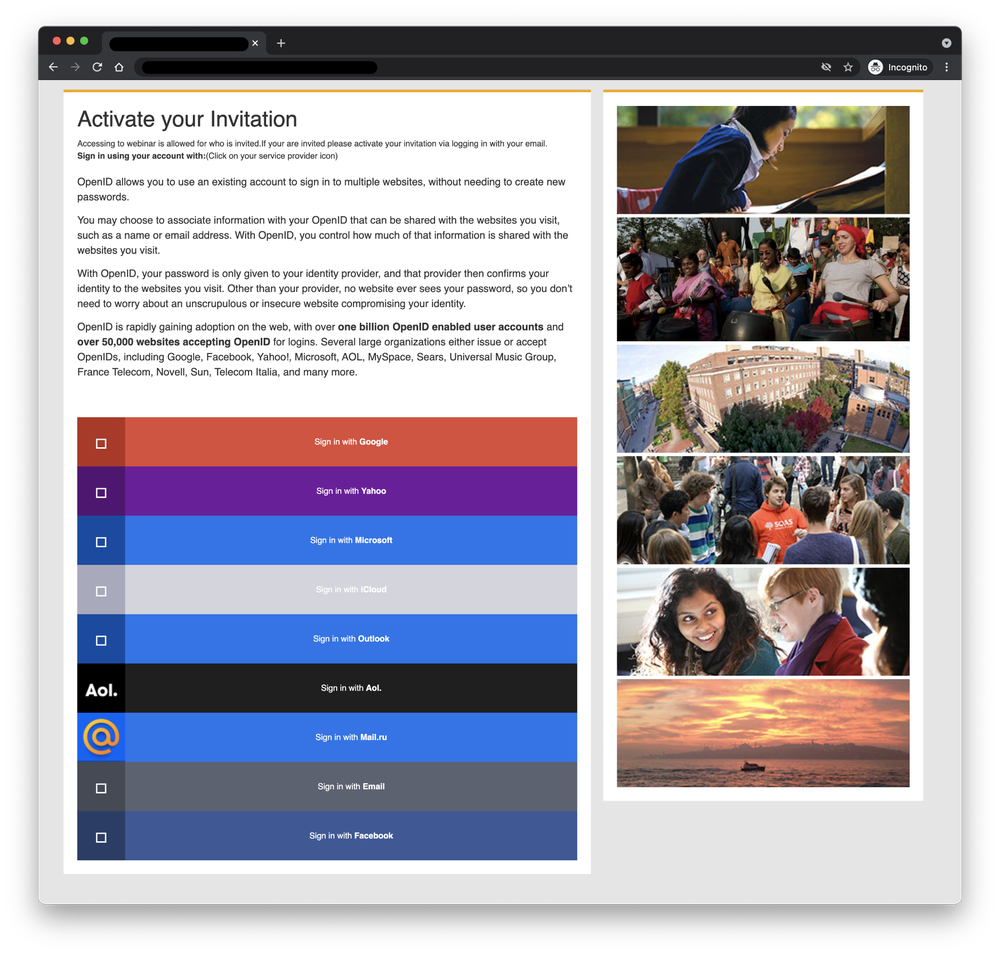
Hijacked websites used for credential phishing attacks
In early 2021, APT35 compromised a website affiliated with a UK university to host a phishing kit. Attackers sent email messages with links to this website to harvest credentials for platforms such as Gmail, Hotmail, and Yahoo. Users were instructed to activate an invitation to a (fake) webinar by logging in. The phishing kit will also ask for second-factor authentication codes sent to devices.
APT35 has relied on this technique since 2017 — targeting high-value accounts in government, academia, journalism, NGOs, foreign policy, and national security. Credential phishing through a compromised website demonstrates these attackers will go to great lengths to appear legitimate – as they know it’s difficult for users to detect this kind of attack.